Access Authorization
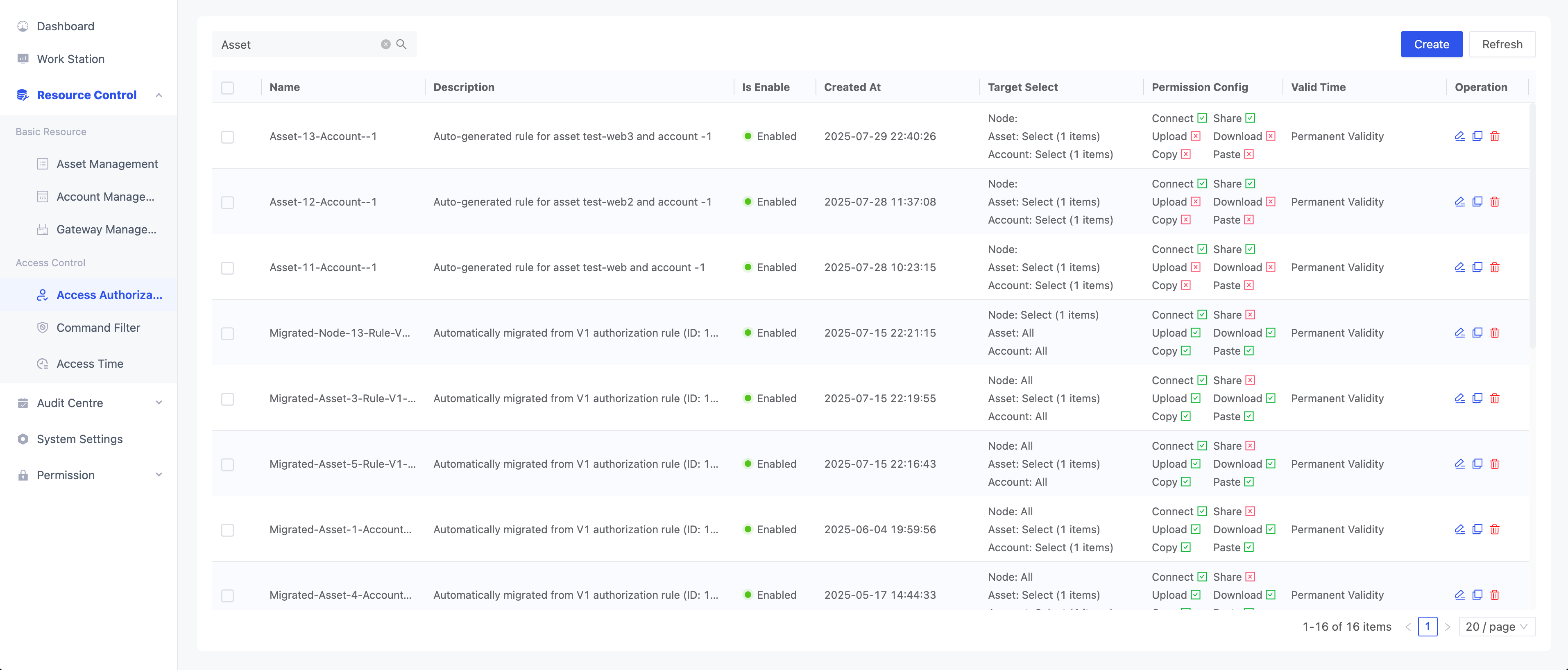
The Access Authorization page is used for centralized management of node, asset, and account access permissions, enabling a unified and standardized authorization system.
With six permission controls (connect, share, upload, download, copy, paste), combined with security policies such as access time, sensitive command interception, and IP whitelisting, administrators can efficiently create and adjust authorization rules to meet compliance and security requirements for various business scenarios.
Users can perform detailed batch configurations on this page, or use the Resource Control - Asset Management or Resource Control - Account Management pages for quick authorization setup. All authorization data will be displayed on this page, regardless of the configuration method.
Create Access Authorization
Click the “Create” button in the upper right corner to add a new access authorization.
Access Authorization Parameter Description
| Category | Parameter | Description | Required |
|---|---|---|---|
| Basic Info | Name | Name of the authorization policy, for easy management and lookup | ✓ |
| Description | Brief description of the authorization policy | ||
| Valid Time | Time period during which the authorization policy is effective; leave blank for permanent | ||
| Is Enable | Enable or disable the current authorization policy | ||
| Target Select | Folder Select |
| |
| Asset Select |
| ||
| Account Select |
| ||
| Access Control | Authorization Role | Specify the user role for this authorization | ✓ |
| Permission Config | Select required permissions to define allowed operations. Note: Upload and download apply to SSH/RDP protocols; copy and paste apply to RDP protocol. | ✓ | |
| Access Time | Select or customize access time templates, supporting multiple time zones and periods. See Resource Control - Access Time for details. | ||
| Command Filter | Configure interception of high-risk or sensitive commands to enhance system security. See Resource Control - Command Filter for details. | ||
| IP Whitelist | Set allowed IP addresses; multiple IPs can be configured |